Ef persónulegar upplýsingar á borð við lykilorð fyrir innskráningu fara ódulrituð yfir internetið, er mjög auðvelt að hlera þær. Ef þú ert að skrá þig inn á eitthvað vefsvæði, ættirðu að ganga úr skugga um að vefsvæðið bjóði HTTPS-dulritun, sem verndar gegn þessari tegun hlerana. Þú getur sannreynt þetta á staðsetningastikunni: ef tengingin þín er dulrituð, byrjar slóðin með “https://” í stað bara “http://”.
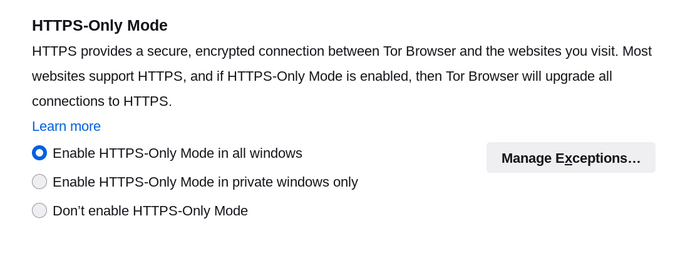
Einungis-HTTPS-hamur í Tor-vafranum
Einungis-HTTPS-hamur þvingar allar tengingar við vefsvæði til að nota örugga dulritaða tengingu sem kallast HTTPS.
Flest vefsvæði styðja nú þegar HTTPS; sum styðja bæði HTTP og HTTPS.
Að virkja þennan ham tryggir a allar tengingar þínar við vefsvæði séu uppfærðar í að nota HTTPS og séu þar af leiðandi öruggar.
Sum vefsvæði styðja einungis HTTP og þá er ekki hægt að uppfæra tenginguna. Ef HTTPS-útgáfa af vefsvæðinu er ekki til staðar, muntu sjá síðu með “Örugg tenging ekki tiltæk”:
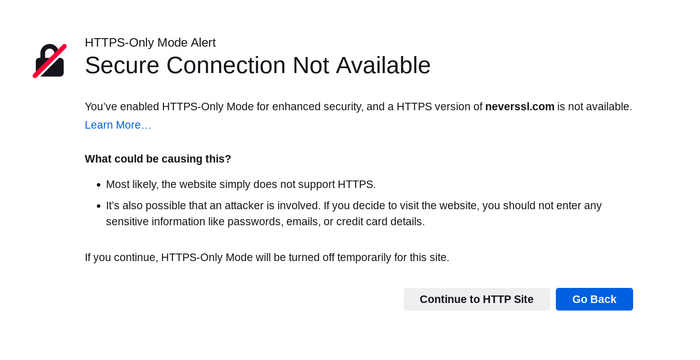
Ef þú smellir á 'Halda áfram á HTTP-vefsvæði', samþykkir þú áhættuna og munt í framhaldinu skoða HTTP-útgáfu vefsvæðisins. Slökkt verður tímabundið á Einungis-HTTPS-ham fyrir það vefsvæði.
Smelltu á 'Til baka' hnappinn ef þú vilt forðast ódulrituðaðar tengingar.
Cryptocurrency safety
Tor Browser presents a security prompt if a cryptocurrency address has been copied from an insecure HTTP website.
The cryptocurrency address could have been modified and should not be trusted.
Clicking 'Reload Tab with a New Circuit' will attempt to load a secure version of the website with a new Tor circuit.
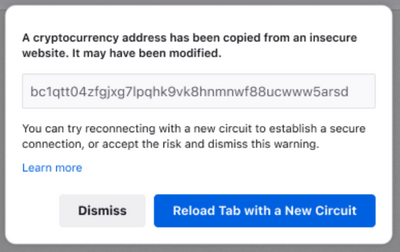
If you click 'Dismiss' you accept the risk and the cryptocurrency address will be copied to the clipboard.
Hvernig HTTPS-dulritun og Tor virka í Tor-vafranum til að bæta nafnleysi og vernd einkagagna
Eftirfarandi skýringamynd sýnir hvaða upplýsingar eru sýnilegar milliliðum með og án Tor-vafrans með HTTPS-dulritun:
- Smelltu á “Tor”-hnappinn til að sjá hvaða gögn eru sýnileg eftirlitsaðilum þegar þú ert að nota Tor. Hnappurinn verður grænn til að gefa til kynna að kveikt sé á Tor.
- Smelltu á ““HTTPS””-hnappinn til að sjá hvaða gögn eru sýnileg eftirlitsaðilum þegar þú ert að nota HTTPS. Hnappurinn verður grænn til að gefa til kynna að HTTPS sé virkt.
- Þegar báðir hnapparnir eru grænir, sérðu gögnin sem eru sýnileg milliliðum þegar þú notar bæði þessi verkfæri.
- Þegar báðir hnapparnir eru gráir, sérðu gögnin sem eru sýnileg milliliðum þegar þú notar hvorugt þessara verkfæra.
MÖGULEGA SÝNILEG GÖGN
-
www.vefur.is
-
Vefsvæðið sem verið er að skoða.
-
notandi / lykilorð
-
Notandanafn og lykilorð sem notuð eru við auðkenningu.
-
gögn
-
Gögn sem verið er að senda.
-
staður
-
Netstaðsetning tölvunnar sem notuð er til að heimsækja vefsvæðið (opinbert IP-vistfang).
-
tor
-
Hvort verið er að nota Tor eða ekki.