Understanding browser fingerprinting
Browser fingerprinting is the systematic collection of information about the web browser to make educated guesses about its identity or characteristics.
Each browser's settings and features create a "browser fingerprint".
Most browsers inadvertently create a unique fingerprint for each user, which can be tracked across the internet.
For more in-depth information on browser fingerprinting, refer to these articles on the Tor Blog: Browser Fingerprinting: An Introduction and the Challenges Ahead and Tor Browser: a legacy of advancing private browsing innovation.
Why browser fingerprinting threatens online privacy?
First, there is no need to ask for permissions from the user to collect this information.
Any script running in the browser can silently build a fingerprint of the device without users even knowing about it.
Second, if one attribute of the browser fingerprint is unique or if the combination of several attributes is unique, the device can be identified and tracked online.
This means that even without cookies, a device can be tracked using its fingerprint.
How Tor Browser mitigates fingerprinting
Tor Browser is specifically engineered to minimize the uniqueness of each user's fingerprint across various metrics.
While it is practically impossible to make all Tor Browser users identical, the goal is to reduce the number of distinguishable "buckets" for each metric.
This approach makes it harder to track individual users effectively.
Certain attributes, like the operating system and language, are necessary for functionality and cannot be completely hidden or spoofed.
Instead, Tor Browser limits the variety within these attributes to reduce distinctiveness.
For example, it limits font enumeration and applies character fallback, standardizes screen and window sizes using letterboxing, and restricts the variety of requested languages to a small, predefined set.
The key goal of Tor Browser's anti-fingerprinting protections is to make it significantly more challenging to gather enough information to uniquely identify users, thereby enhancing privacy without compromising necessary functionality.
Anti-fingerprinting features in Tor Browser
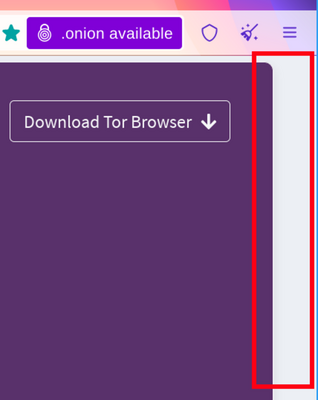
Letterboxing
To prevent fingerprinting based on screen dimensions, Tor Browser starts with a content window rounded to a multiple of 200px x 100px.
The strategy here is to put all users in a couple of buckets to make it harder to single them out.
That works so far until users start to resize their windows (e.g. by maximizing them or going into fullscreen mode).
Tor Browser ships with a fingerprinting defense for those scenarios as well, which is called Letterboxing, a technique developed by Mozilla and presented in 2019.
It works by adding margins to a browser window so that the window is as close as possible to the desired size while users are still in a couple of screen size buckets that prevent singling them out with the help of screen dimensions.
In simple words, this technique makes groups of users of certain screen sizes and this makes it harder to single out users on basis of screen size, as many users will have same screen size.
User-Agent and Operating System spoofing
The User-Agent string is a value websites can use to identify details about your browser, operating system (OS), CPU architecture, vendor, and version.
Since this information can reveal which OS or device a user is using, it has been a vector for browser fingerprinting, allowing websites or trackers to potentially single out users.
Tor Browser addresses this by spoofing the User-Agent. Users cannot choose a specific operating system or attempt to imitate every possible platform.
Instead, Tor Browser standardizes User-Agent values to reduce uniqueness and avoid creating a false sense of privacy:
- All Windows appear as Windows 10.
- All macOS appear as OS X 10.15.
- All Android as Android 10.
- All other systems like all Linux distributions (including Tails and Qubes), *BSD and other operating systems are grouped together and reported as "Linux running X11".
- All the other details (such as the architecture) are also normalized per-platform.
In this case, the fingerprint resistance strategy in Tor Browser is to protect real values of the User-Agent by spoofing, but also have a large enough user set.
User-Agent is sent to websites as an HTTP header, and it is available to JavaScript as navigator.userAgent.
Inconsistencies in these values can trigger anti-bot and anti-fraud systems into categorizing Tor users as a bot, and deny their requests, which in turn affects usability for Tor Browser users.
Some privacy tools or users suggest that making all users appear as Windows would offer the best cover.
However, perfectly spoofing across all browser contexts is not possible and active fingerprinting methods (using fonts, features, behavior, with or without JavaScript, etc.) can often be used to infer aspects of the hardware or operating system.
Tor Browser does not let users select which OS they appear to be.
This is intentional: any option to choose would only make users more unique and thus easier to fingerprint.
The small set of standardized options is key to keeping users blended together, maximizing privacy for everyone.
Other anti-fingerprinting features
In addition to letterboxing, Tor Browser employs many other features to mitigate browser fingerprinting and protect user privacy.
These features include Canvas image extraction blocking, NoScript integration, and first-party isolation.
For a complete list of features, please read the Tor Browser design and implementation document.