Comprendere il browser fingerprinting
Il Browser fingerprinting è la raccolta sistematica di informazioni riguardanti il browser web al fine di formulare ipotesi plausibili circa la sua identità o le sue caratteristiche.
Tutte le impostazioni e funzionalità del browser creano un "browser fingerprint".
La maggior parte dei browser crea inavvertitamente un'impronta digitale unica per ogni utente, che può essere tracciata su Internet.
Per informazioni più approfondite sul fingerprinting del browser, consultare questi articoli del Tor Blog: Browser Fingerprinting: An Introduction and the Challenges Ahead e Tor Browser: a legacy of advancing private browsing innovation.
Perché il browser fingerprinting minaccia la privacy online?
Innanzitutto, non c'è la necessità di chiedere il permesso all'utente per effettuare la raccolta di questa informazione.
Ogni script attivo nel browser può costruire silenziosamente un fingerprint del dispositivo senza che l'utente se ne accorga.
In secondo luogo, se un attributo dell'impronta digitale del browser è unico o se la combinazione di più attributi è unica, il dispositivo può essere identificato e tracciato online.
Ciò significa che anche senza cookie, un dispositivo può essere tracciato utilizzando la sua impronta digitale.
Come Tor Browser riduce il fingerprinting
Tor Browser è specificamente progettato per ridurre al minimo l'unicità dell'impronta digitale di ciascun utente attraverso varie metriche.
Sebbene sia praticamente impossibile rendere identici tutti gli utenti di Tor Browser, l'obiettivo è ridurre il numero di “secchi” distinguibili per ogni metrica.
Questo approccio rende più difficile tracciare efficacemente i singoli utenti.
Alcune proprietà, come il sistema operativo e la lingua, sono necessarie per le funzionalità e non possono essere completamente nascoste o camuffate.
Invece, Tor Browser limita la varietà di questi attributi per ridurre la distintività.
Ad esempio, limita l'enumerazione dei caratteri e applica il fallback dei caratteri, standardizza le dimensioni dello schermo e delle finestre utilizzando il letterboxing e limita la varietà delle lingue richieste a un piccolo insieme predefinito.
L'obiettivo principale delle protezioni anti-fingerprinting di Tor Browser è quello di rendere significativamente più difficile la raccolta di informazioni sufficienti a identificare univocamente gli utenti, migliorando così la privacy senza compromettere le funzionalità necessarie.
Funzionalità anti-fingerprinting in Tor Browser
Letterboxing
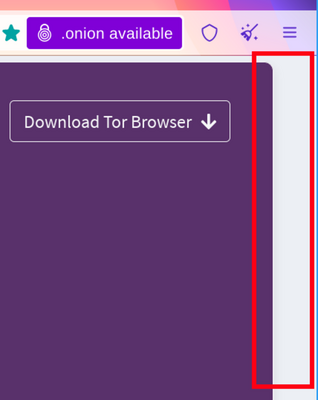
Per evitare il fingerprinting basato sulle dimensioni dello schermo, Tor Browser inizia con una finestra di contenuto arrotondata a un multiplo di 200px x 100px.
La strategia consiste nel raggruppare tutti gli utenti in un paio di gruppi per rendere più difficile individuarli.
Finora funziona, finché gli utenti non iniziano a ridimensionare le finestre (ad esempio, massimizzandole o passando alla modalità a schermo intero).
Tor Browser viene fornito con una difesa di fingerprinting anche per questi scenari, che si chiama Letterboxing, una tecnica sviluppata da Mozilla e presentata nel 2019.
Funziona aggiungendo margini alla finestra del browser, in modo che la finestra si avvicini il più possibile alle dimensioni desiderate, mentre gli utenti si trovano ancora in un paio di gruppi di dimensioni dello schermo che impediscono di individuarli con l'aiuto delle dimensioni dello schermo.
In parole povere, questa tecnica crea gruppi di utenti di determinate dimensioni dello schermo e rende più difficile individuare gli utenti in base alle dimensioni dello schermo, poiché molti utenti avranno le stesse dimensioni.
Altre funzionalità anti-fingerprinting
Oltre al letterboxing, Tor Browser impiega molte altre funzioni per attenuare il fingerprinting del browser e proteggere la privacy degli utenti.
Queste caratteristiche includono il blocco dell'estrazione delle immagini di Canvas, l'integrazione di NoScript, lo spoofing dell'agente utente e l'isolamento di prima parte.
Per un elenco completo delle funzionalità, leggere il documento di progettazione e implementazione di Tor Browser.